Exposed Secrets in Public Repos: A New Frontier in Threat Intelligence
Why hardcoded credentials in GitHub, GitLab, and Bitbucket are becoming the primary entry point for modern cyberattacks.
Whiteintel Team
Intelligence Division
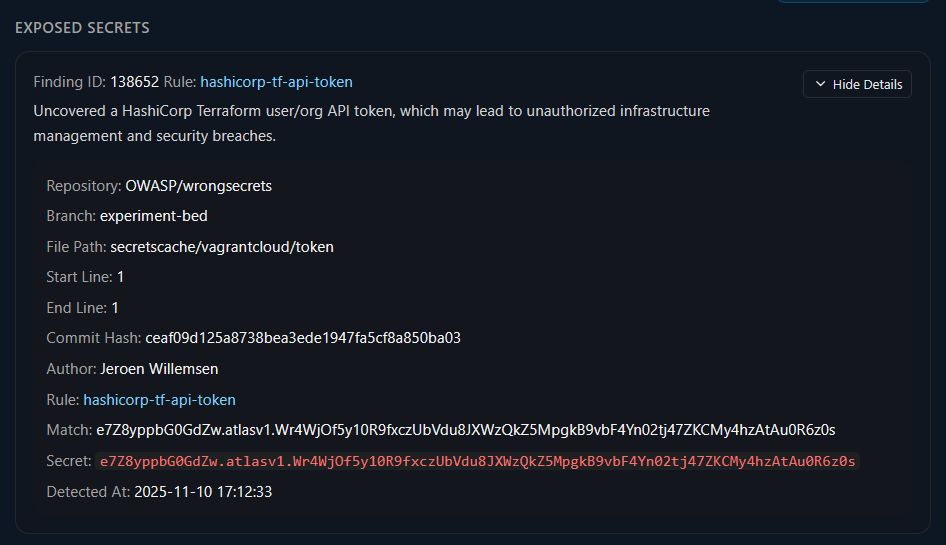
In the race to deploy code faster, developers often bypass security protocols. The result? A massive proliferation of hardcoded API keys, database credentials, and private certificates inadvertently pushed to public repositories. This negligence has birthed a new frontier in threat intelligence: passive reconnaissance via public commits.
The Scale of the Problem
Public repositories like GitHub, GitLab, and Bitbucket host billions of lines of code. While they are invaluable for collaboration, they are also a goldmine for threat actors. A simple mistake--forgetting to add a .env file to .gitignore--can expose an organization's entire cloud infrastructure in seconds.
Recent analysis indicates that over 10 million secrets were leaked in public commits in 2024 alone. These aren't just low-level tokens; they often include:
-
AWS Access Key IDs & Secret Keys
-
Stripe & PayPal Live API Keys
-
Google Cloud Service Account JSONs
-
Private SSH Keys (id_rsa)
How Attackers Exploit This
The window of opportunity for an attacker is shrinking. It is no longer about humans manually searching for "password"; it is about automation. Threat actors deploy sophisticated scrapers that monitor the "firehose" of public events in real-time.
When a developer pushes code containing a secret, bots detect it within seconds.
The Attack Lifecycle
- Commit: Developer pushes code with `AWS_SECRET_ACCESS_KEY`.
- Detection: Attacker's bot scans the public feed and identifies the pattern.
- Validation: The bot automatically tests the key against the API to check permissions (e.g., `sts:GetCallerIdentity`).
- Persistence: If valid, the attacker creates a backdoor user or spins up crypto-mining instances.
Whiteintel's Approach: Proactive Monitoring
Traditional security tools scan repositories after they are connected to an organization. However, shadow IT means developers often use personal accounts for work projects. Whiteintel bridges this gap by monitoring the entire public commit stream for keywords associated with your organization's domains and assets.
Our "Repository Intelligence" module allows security teams to:
- Detect corporate emails used in personal GitHub commits.
- Identify leaked internal subdomains in configuration files.
- Receive alerts instantly when a high-entropy string is associated with your brand.

Conclusion
As organizations secure their perimeter, the "human element" remains the weakest link. Public repositories are the new perimeter. Ignoring them is akin to leaving the front door open while locking the windows. By leveraging automated intelligence to monitor these external sources, organizations can detect and revoke leaked credentials before they result in a catastrophic breach.
Protect your assets today. Learn more about our Repository Monitoring at: whiteintel.io